Cyber Security (MSc)
Programme structure
The programme consists of four phases: conceptualisation, specialisation, electives and thesis.
For detailed information on the courses and curricula, see the e-Prospectus. Please note that this guide applies to the current academic year, which means that the curriculum for next year may differ slightly.
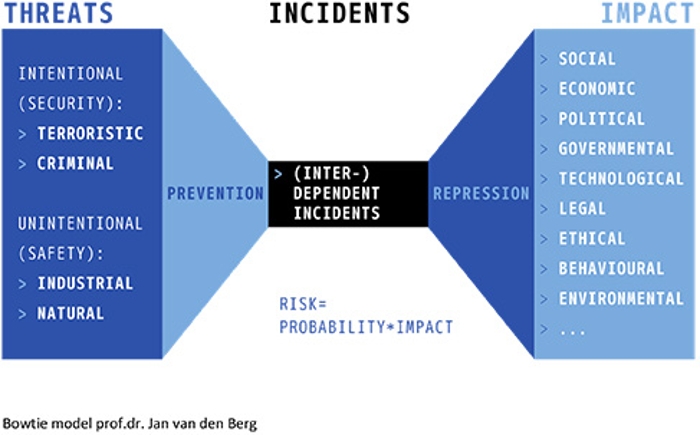
In the first phase you will get a general introduction into cyber security based on the bowtie model.
- In the first module (Introduction to cyberspace) you will explore what cyberspace entails by conceptualizing cyberspace and analyzing several definitions of it. The three-layer model for conceptualizing cyberspace forms the guide for this course. In addition fundamental concepts that are central to understanding and reasoning about cyberspace are covered, as well as the link to cyber security and related risks.
- In the second module (Introduction to cyber security) relations between safety, security, cyber security and cyberspace are explored in depth. Special attention is paid to regulation and how this relates to cyber security. The notion and functioning of cyber norms completes this introduction into cyber security governance. The course also zooms in on the governance of ICT systems – including critical infrastructures – and the Internet.
- You will finish the first semester with Cyber Risk. This module complements the second module and provides students with a broader understanding of risk as conceived in the social sciences and helps students understand the strengths and limitations of common risk management approaches.
For detailed information on the courses and curricula, see the e-Prospectus (search for Cyber Security in Programmes). Please note that this guide applies to the current academic year, which means that the curriculum for next year may differ slightly.
The second semester starts with the compulsory modules Legal Perspectives on Cyber Security (capita selecta on legal aspects) and Cyber Security Economics (on the relation between economic theory and practice and cyber security).
After this compulsory module you choose a specialisation: 1. the technical track or 2. the governance track.
You can choose two of the four electives that are offered. Examples of electives in previous years are:
- Actors & Behaviour in Cyberspace
- Data Mining
- Industrial Control Systems & Critical Infrastructures
- Cyber Crisis Management & Communication
The number of electives can vary, depending on the number of participants and their interests and backgrounds. The subjects of the electives can also vary, depending on current issues. For some electives, admission may depend on prior education and knowledge.
The programme concludes with a thesis. You will identify a complex issue or case from practice in the field of digital security. You will then individually research a partial aspect that connects to your prior knowledge and interests, and will include your insights and reflections in the thesis.
Some of the courses highlited
This course takes place in the technical track. In the first part of the course attention will be paid to present ICT and Industrial Control Systems as well as networks. Specific attention will be paid to their attacks and vulnerabilities. The second part of the course handles the security principles and the available technical security measures and their meaning for cyber security, both repressive and preventive. The basic security mechanisms as confidentiality, identification, integrity, authentication and authorisation are given. After a short introduction to (a)symmetric cryptography and key management the various cryptographic algorithms and methods for the various security mechanisms are considered as well as their corresponding (inter)national standards. Attention is paid to architecture models and standards and the technical aspects of the management of security services.
The role of datamining techniques for detection of anomalies and potential fraud is considered. Although most security measures are digital, finally physical security measures are unavailable, e.g. secure key storage. We also look at security modules and the physical security of devices and attacks on e.g. smartcards.
This course takes places in the governance track. ‘Contested spaces’, where a state is unable or unwilling to exert its authority, have frequently been defined as threats to international security in the past twenty years. These were often geographical areas synonymous with ‘failed states’, where non-state actors such as terrorists or criminal organisations would seek sanctuary. According to public perception cyberspace has now become one of these ‘ungoverned spaces’, out of reach for governments and businesses alike. Cybercrime and cyber terrorism have proliferated as a result, and according to some the threat of cyber war looms ahead. This cyber-governance module will look at where responsibility for cyber security in the public-private-individual triangle is placed and how government institutions have shared, distributed or obtained cyber tasks and duties. Strategies and doctrines will also be covered, and how they combine with traditional state responsibilities such as defence and intelligence (espionage).
In practice, however, internet is not so much ungoverned as subjugated to alternative forms of governance, often by non-state actors. Although relatively little has as yet been written in academia on cyber governance, this module will explore the customary theories from public administration and legal perspectives.
Cyberspace also has important repercussions for conflict studies. Traditional concepts such as sovereignty, power, war, espionage and terrorism could face fundamental changes as global internet connectivity and dependence continues to grow. This module will look at competing views on cyber threats (from a ‘digital pearl harbour’ to cyber-operations in support of conventional military attacks), working through definitions, concepts and policies to sketch some of the possible implications for future inter and intra-state relations.

